
Important Security Alert: Issue Found in React (Common Website Technology)
A serious security fault has been discovered in a piece of software called React, which many websites and online services use behind the scenes. This…
Cyber security researchers at Palo Alto Unit 42 have discovered a new Python version of the NodeStealer that can take over Facebook Business Accounts.
Based on the available data, the primary way the data stealer spread was through a phishing campaign that occurred in December 2022. In this campaign, two data stealer versions, Variant #1 and Variant #2, were delivered.
The campaign’s focus was to deceive people with business advertisements. The attackers utilised various Facebook pages, and user accounts to post enticing information, leading victims to download a link from familiar cloud file storage services. Once they clicked on the link, a .zip file containing the harmful data stealer program was downloaded to their computer.
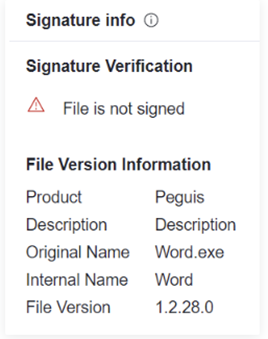
Variation #1
The first variation of the data stealer was called word.exe, and it had the following features;
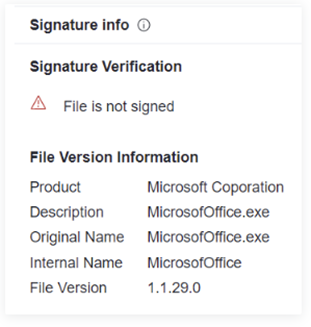
Variation #2
The second variation of the data stealer was called MicrosoftOffice.exe, and it had the following features;
The variations share some of their features but differ in some areas. See below the differences between the variants:

The suspected threat actor behind this campaign has Vietnamese origins and equipped the new variants with capabilities to steal crypto currencies, function as downloaders, and fully take over Facebook Business Accounts. The consequences of this malware can be severe for both individuals and organisations, leading to financial losses and damage to their reputations.
To combat this threat, we urge all organisations to review their security policies and take note of the indicators of compromise provided in Unit 42’s report. For Facebook Business Account owners, using strong passwords and enabling multifactor authentication is crucial to enhance security. Additionally, educating your organisation on phishing tactics, particularly modern and targeted approaches that exploit current events, business needs, and other appealing topics, is essential to stay vigilant against such attacks.