
Important Security Alert: Issue Found in React (Common Website Technology)
A serious security fault has been discovered in a piece of software called React, which many websites and online services use behind the scenes. This…
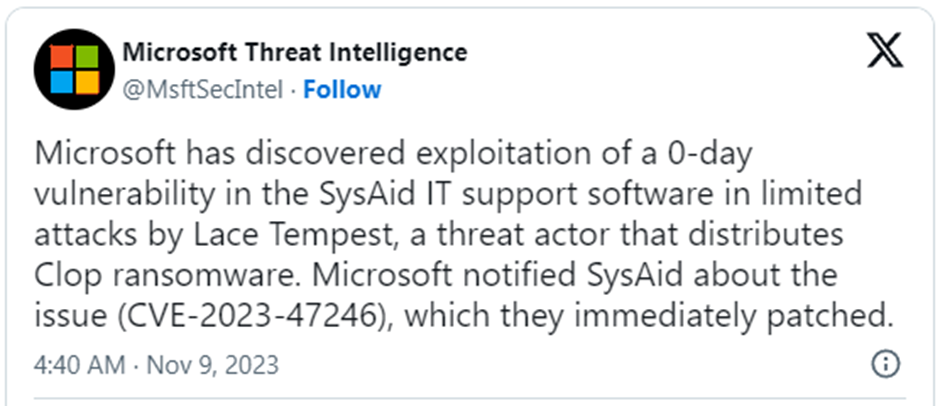
Hackers are taking advantage of a newly discovered weakness in a software product called SysAid, which companies use to manage their IT services. This vulnerability allows attackers to access these companies’ servers, where they can steal data and install a type of malicious software called Clop ransomware.
Clop ransomware is known for exploiting vulnerabilities in widely used software, and recent examples include MOVEit Transfer, GoAnywhere MFT, and Accellion FTA.
The specific weakness in SysAid is identified as CVE-2023-47246. It was found on November 2 when hackers used it to access SysAid servers located on-premises, not in the cloud.
The Microsoft Threat Intelligence team discovered that hackers were actively using this vulnerability to attack SysAid and informed SysAid about the security issue. Microsoft also found that the same vulnerability was previously exploited by a group of hackers known as Lace Tempest (also called Fin11 and TA505) again to deploy Clop ransomware.
Earlier this week, SysAid released a report explaining that the vulnerability identified as CVE-2023-47246 is a path traversal vulnerability. This flaw allows unauthorised individuals to run their code without permission. SysAid also provided technical details about the attack, which were uncovered through an investigation by the incident response company Profero.
The attackers exploited this zero-day flaw by uploading a Web Application Resource (WAR) archive containing a webshell into the webroot of the SysAid Tomcat web service. This action allowed them to execute additional PowerShell scripts and introduce the GraceWire malware. The malware was cleverly injected into legitimate processes like ‘spoolsv.exe,’ ‘msiexec.exe,’ or ‘svchost.exe.’
According to the report, the malware loader, known as ‘user.exe,’ actively checks running processes to ensure that Sophos security products are not on the compromised system.
After discovering the vulnerability, SysAid acted swiftly to create a fix for CVE-2023-47246, and this solution is now available through a software update. It is crucial for all SysAid users to update to version 23.3.36 or later to ensure their systems are secure.
For system administrators, please follow these steps to check for any signs of compromise:
1. Inspect SysAid Tomcat Webroot: Look for unusual files, especially those with extensions like WAR, ZIP, or JSP and anomalous timestamps.
2. Check for WebShell Files: Examine the SysAid Tomcat service for unauthorised WebShell files and inspect JSP files for potentially malicious content.
3. Review Logs: Look for unexpected child processes from Wrapper.exe, which may indicate the use of WebShells.
4. Examine PowerShell Logs: Check for script executions aligning with the attack patterns described.
5. Monitor Key Processes: Keep an eye on processes such as spoolsv.exe, msiexec.exe, and svchost.exe for signs of unauthorised code injection.
6. Apply Indicators of Compromise (IOCs): Use the provided IOCs to identify any signs of the vulnerability being exploited.
7. Search for Attacker Commands: Look for evidence of specific attacker commands that suggest a system compromise.
8. Run Security Scans: Conduct security scans for known malicious indicators related to the vulnerability.
9. Check for Connections: Examine for connections to the listed Command and Control (C2) IP addresses.
10. Watch for Cleanup Signs: Be vigilant for signs of attacker-led cleanup activities aimed at concealing their presence.
SysAid’s report includes indicators of compromise, such as filenames, hashes, IP addresses, file paths, and commands the threat actor uses. Utilise these indicators to detect or prevent intrusions and enhance the security of your systems.