
Third Sector Membership Competition Launched
To celebrate the launch of our first Cyber and Fraud Centre – Scotland Impact Report, we are delighted to also launch a special competition –…
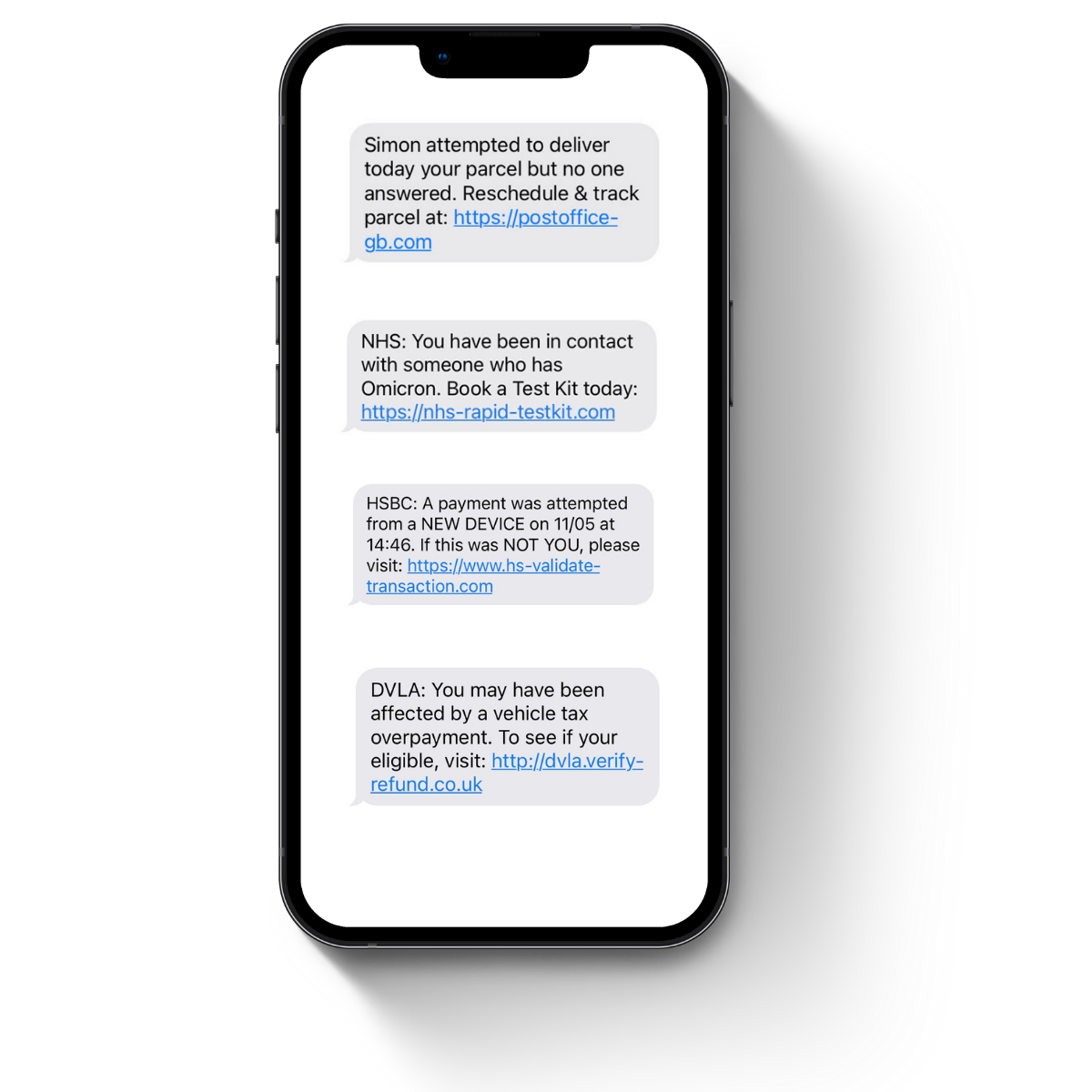
Quick! Your account will expire today if you don’t reactivate it now! There’s a gift card up for grabs too, just click here! Oh, and did I mention that Simon was unable to deliver your parcel?
More phishing attacks are happening now than ever before – it’s estimated that over 3.4 billion phishing emails are sent daily[1] in 2022, and almost half of all emails sent in 2021 were phishing emails[2].
Thankfully, education on phishing attacks and how to spot them is rising. Generally, everyone is given the same advice – Check the sender, is it a legitimate email address? Are there obvious spelling mistakes, is the email addressed to you, and are they trying to get you to click on a link or send back personal details? Most advice on spotting phishing attacks boils down to the user doing one key thing – taking a step back and taking the time to think the message through.
Naturally, this is the last thing a scammer wants a potential victim to do. To avoid this, many phishing attacks have taken advantage of the human instinct to act urgently upon bad (or good!) news.
As phishing attacks become more and more sophisticated, being able to spot the language and psychological tactics used within these attacks can be just as important as knowing the typical red flags of a phishing attack.
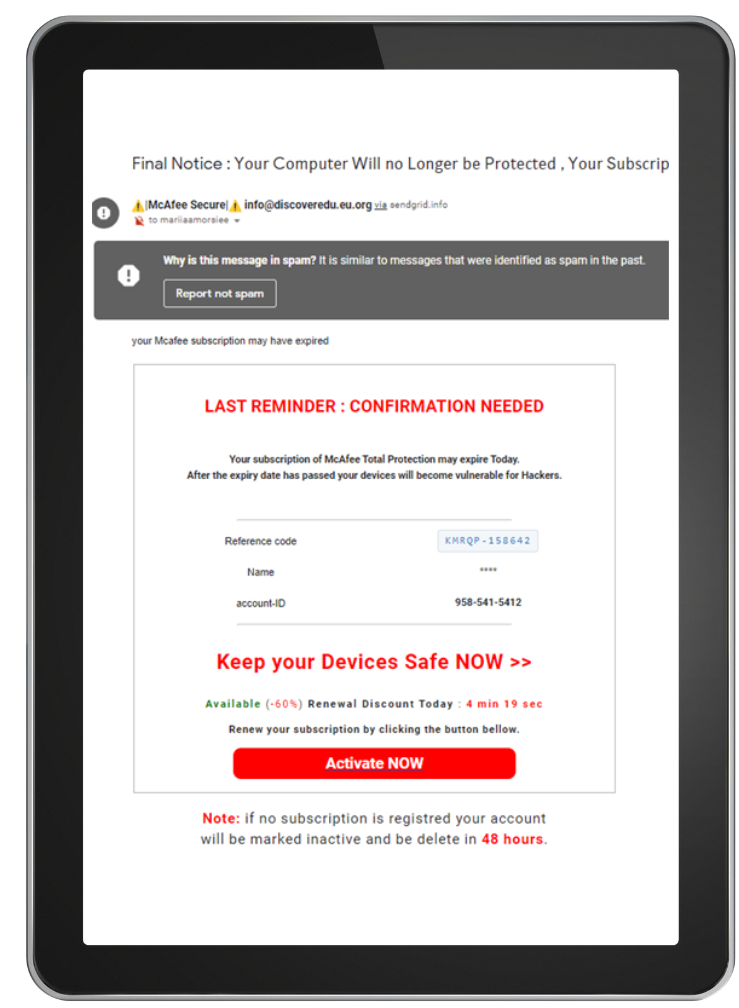
Phishing emails are often centered around the victim being so focused on the message that they don’t notice the typical stand-out features of a phishing attack.
Stress is known to have a huge effect on decision making, and studies have shown that high-stress levels can cause people to pay more attention to the upsides of a situation than the downsides[3].
Scammers have crafted phishing attacks to perfectly create the high-stress levels needed to affect someone’s decision making enough to push them towards falling for the scam. Potential victims will have to weigh up the “urgent” information given to them in an email or text. They’ll often see the upside of being able to immediately renew their account, quickly reship a parcel, or reclaim tax, and chose these positive but fake scenarios that instantly fix the situation instead of taking a moment to consider the legitimacy of the message.
To create this sense of urgency and stress, phishing attacks contain language that drives any reader to want to instantly respond, to the extent that even experts in cyber security will feel their heart jump for a second when first receiving a malicious text. Most generic phishing attacks will use the same urgent language and being able to recognise the terms and phrases used will put a user at less risk of an attack.
[3] https://www.psychologicalscience.org/news/releases/stress-changes-how-people-make-decisions.html

As awareness of phishing attacks grows, scammers are using more and more plausible scenarios that have a high chance of affecting the recipient. The old scenario of a foreign prince in desperate need of money is long gone and has been replaced by the recipient being told their parcel is unable to be delivered, they are eligible for a discount on their rising energy bills, or that they have recently come into contact with someone who tested positive for covid.
Recent news headlines and large events have started becoming a common topic for phishing attacks. Covid-19 is a major example of this, and with over £30 million stolen within the first year of the pandemic[4], it is easy to see why.
Generic phishing scams will often include these features:
Spear phishing attacks, ones that are targeted towards a specific business, charity, or person, will often be made to look exactly like a regular business email from a customer or co-worker, possibly asking for a form to be filled in or asking for help with a job. These attacks are made to look as mundane as possible and can target anyone within a business.
About Sarah –
Sarah is a second year Abertay University student studying Ethical Hacking full-time. Sarah is part of Abertay’s Women in Cyber Security chapter, where she give talks on cyber security and on what it means to be an ethical hacker with the aim to encourage more females into the cyber security sector.
Sarah’s interest in cyber security and ethical hacking started with a summer course at Cyber First Advanced, and ever since taking part she has been looking to further her knowledge in the area. Sarah also enjoys programming and networking, and is eager to learn more about programming from a security perspective.
In Sarah’s free time, she enjoys running and walking in the countryside and also enjoys taking part in a few of Abertay’s societies, such the ethical hacking society and the programming society.